There are several types of DDoS attacks, including:
Volume-Based Attacks
Floods the target with a massive amount of traffic, such as UDP floods and ICMP floods.
Protocol Attacks
Exploits vulnerabilities in network protocols, like SYN floods that overwhelm server resources by initiating multiple connection requests.
Application Layer Attacks
Targets specific applications or services, overwhelming web servers or databases with requests, such as HTTP floods.
By understanding the nature of DDoS attacks and implementing proactive protection strategies, organizations can effectively mitigate the impact of these disruptive cyber threats, safeguarding their online presence and ensuring uninterrupted service delivery to users worldwide.
Network Security Measures
Including firewalls, routers with traffic filtering capabilities, and intrusion prevention systems (IPS).
DDoS Mitigation Services
Provided by specialized vendors offering real-time traffic monitoring and filtering to distinguish legitimate traffic from malicious attacks.
Scalable Infrastructure
Provided by specialized vendors offering real-time traffic monitoring and filtering to distinguish legitimate traffic from malicious attacks.
Regular Audits and Updates
Keeping systems and software patched and up-to-date to minimize vulnerabilities.
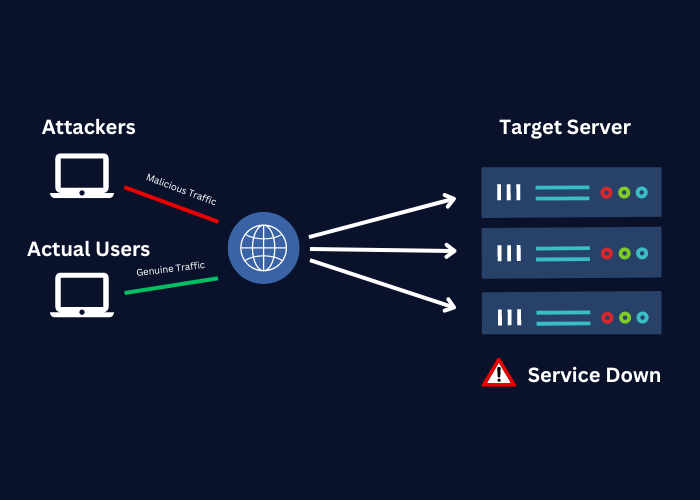
A DDoS (Distributed Denial of Service) attack aims to overwhelm your website or network with malicious traffic, causing downtime and disrupting operations. This can severely impact your revenue and reputation. At The Noble Hackers, we specialize in defending against DDoS attacks to ensure your online services remain secure and accessible.
We deploy cutting-edge DDoS mitigation strategies to safeguard your infrastructure. Our approach includes real-time traffic analysis, advanced filtering techniques, and the use of specialized tools to detect and block malicious traffic swiftly. This proactive defence helps mitigate the impact of DDoS attacks, ensuring uninterrupted service for your customers.
To prepare for potential DDoS threats, it’s essential to implement robust defences. The Noble Hackers provide comprehensive DDoS protection solutions tailored to your business needs. We assess your infrastructure, recommend suitable mitigation techniques, and assist in developing incident response plans. By partnering with us, you can fortify your defences and minimize the risk of disruption from DDoS attacks.
